As journalists, we often report on secret meetings — closed to everyone but the participants. I dedicated “Breakway” to “anyone who has ever wondered what happens behind closed doors.” I did that mostly because I always wonder what decisions are made and deals reached behind closed doors.
As journalists, we often report on secret meetings — closed to everyone but the participants. I dedicated “Breakway” to “anyone who has ever wondered what happens behind closed doors.” I did that mostly because I always wonder what decisions are made and deals reached behind closed doors.
For my latest assignment, I actually got to go behind closed doors. I went behind armed guards too. The U.S. Army War College permitted me to attend a policy planning session on “Cyber Sovereignty.” The three-day workshop brought together top minds from all branches of the military, from the private sector and from academia.
The event allowed me to provide readers of the Tribune-Review exclusive access to these deliberations about the future of our nation’s cybersecurity. I also discussed my findings on 90.5 WESA-FM, Pittsburgh’s NPR station.
My stories…

Summer Fowler
When Summer Fowler goes to sleep, the Cranberry mother of three knows computer hackers around the world are working through the night to undo the defenses she spends her days building.
Fowler, 37, is deputy technical director for cybersecurity solutions at CERT, the nation’s first computer emergency response team, at Carnegie Mellon University’s Software Engineering Institute. She works with Pentagon soldiers, intelligence directors and corporate titans to help them identify key electronic assets, secure them from cyber attacks and plan for what happens if someone steals them.
But at the end of the day, once her children are tucked into bed, Fowler wonders what the impact would be from a real cyber 9/11 attack…Read more.

Richard Pethia
Pittsburgh’s prominent and growing role as a national center for cybersecurity started with a chance encounter more than 25 years ago.
On Nov. 2, 1988, researchers at the Defense Advanced Research Projects Agency, or DARPA, were ending the workday when calls started coming in from across the country. Something was slowing computer connections on the early Internet — moving freely, guessing passwords to break into systems, accessing files and quickly replicating.
About 60,000 people were connected to the infant web in those days, and many knew each other. The idea had been to build a network for military operations and research that could withstand attacks on any one or two individual computers.
But as the so-called Morris worm spread, questions about security quickly arose. The first computer virus had been unleashed…Read more.
 CARLISLE — Rarely has a raunchy movie done so much to change the world.
CARLISLE — Rarely has a raunchy movie done so much to change the world.
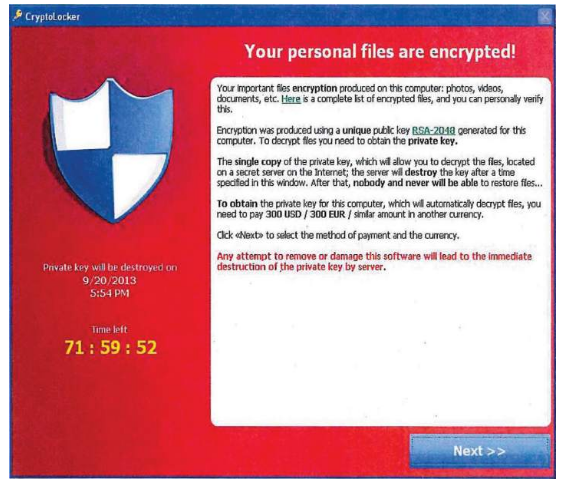
When hackers broke into computer systems at Sony Pictures Entertainment in a failed attempt to stop the release of “The Interview” late last year, the cyberattack changed the way top American military policymakers look at online warfare, experts say.
Electronic skirmishes that had played out quietly among computer technicians at a hacked company and a federal agency contacted for advice instead went all the way to the Oval Office, as President Obama blamed the Sony incident on a nation-state attack by North Korea. Read more.
CARLISLE — If President Obama’s proposed new agency to coordinate federal cybersecurity efforts leads to increased information sharing among government agencies and private companies, that will improve defenses against hack attacks all around, experts gathered here this week said. Read more.
 With the Obama administration striking back at supposed Russian hackers and the Trump administration raising questions, Pittsburgh continues to remain at the center of much of this discussion.
With the Obama administration striking back at supposed Russian hackers and the Trump administration raising questions, Pittsburgh continues to remain at the center of much of this discussion.